

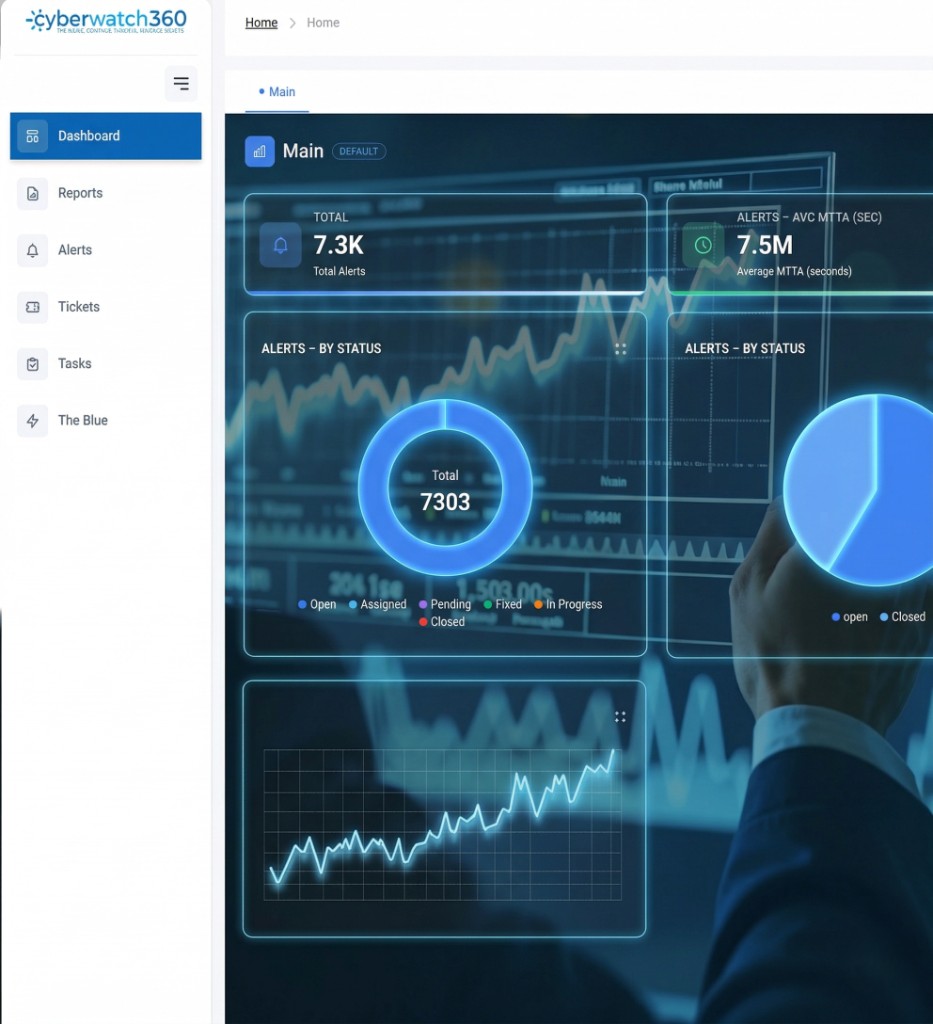
We enhance cybersecurity operations through a smart, unified platform that brings together alerts, ticketing, and Security Operations Center (SOC) work in one place. Using advanced AI and machine learning, we help organizations automate repetitive work, reduce response times, and shrink the effort required to manage incidents—so analysts spend less time on triage and more time stopping real attacks.



Aggregate SIEM, EDR/XDR, firewalls, cloud sources (e.g. AWS GuardDuty, Azure Sentinel), and IDS/IPS into one console—with parsing, normalization, deduplication, and AI-assisted correlation to reduce noise.
Enriched tickets for platforms like ServiceNow and Jira—IOCs, risk scores, MITRE TTP context, assignments by skill and workload—plus structured tasks, Kanban views, SLAs, and notifications across email, Slack, and Microsoft Teams.
Centralized configuration for categories, priorities, statuses, processes, policies, services, and roles—so the same operational model flows from alert triage through task execution and audit-ready logging.
Unlike fixed SOAR scripts (if A then B), agentic AI reasons across signals—e.g. correlating a login with Jira and Slack—to decide next steps. The Zarqaa assistant acts as a virtual L1 analyst: recommendations, routine analysis, and 24/7 coverage without burning out your team.
Cyberwatch360 exists because modern SOCs drown in disconnected tools and alert noise. We combine a unified operations layer with AI that prioritizes real incidents, explains its actions, and scales from lean MSSPs to large regulated enterprises—especially where digital transformation and compliance (e.g. SAMA, national cyber frameworks) raise the bar.
Bring alerts, tickets, and tasks together instead of juggling siloed SIEM, EDR, and ITSM screens—so critical incidents are less likely to be missed or mishandled.
Ingest via REST, webhooks, syslog, or email; normalize fields; deduplicate and correlate; auto-generate enriched tickets with IOCs, risk scores, and MITRE mappings.
Zarqaa reasons across tools and context like a fast, efficient analyst—not a rigid playbook. Every action can be traced in a reasoning log so you trust why an alert was closed as false positive or escalated.
Purpose-built for organizations facing alert overload, fragmented workflows, and talent gaps—from MSSPs needing multi-tenant efficiency to SMEs that need a security copilot without a 24/7 SOC.
Alert coverage goal—no alert left uninvestigated
AI assistant vigilance as a virtual L1 analyst
Targeting the waste in the sorting that consumes the analysts' time